Wifi Theft Prevention Tips


Wi-Fi has become an essential part of our daily lives, and we rely on it to stay connected to the internet. However, many of us may not realize that our WiFi network can be easily compromised by unauthorized users.
In this article, we will explore the question of whether anyone can steal your WiFi and what steps you can take to protect your network.
Can anyone steal your WiFi?
The short answer is yes, anyone with the right tools and knowledge can steal your WiFi. Wi-Fi signals are transmitted through radio waves, which can be intercepted by anyone within range of your network. This means that anyone with a Wi-Fi-enabled device, such as a laptop or smartphone, can potentially connect to your network without your permission.
One of the most common methods used by attackers to steal Wi-Fi is known as “WiFi piggybacking“. This involves using someone else’s WiFi network without their permission, often by simply connecting to an unsecured network or guessing the password to a secured network.
Another common method is known as “WiFi cracking“. This involves using software tools to try and guess your WiFi password or exploit vulnerabilities in your network to gain access.
What are the Risks of someone Stealing your WiFi?
There are several risks associated with someone stealing your WiFi:
- Slow internet speeds: If someone is using your WiFi network, they are effectively sharing your internet bandwidth. This can slow down your internet speeds, making it difficult for you to use your own network.
- Security risks: When someone connects to your Wi-Fi network, they may be able to access your personal information, such as your browsing history, login credentials, and other sensitive data.
- Illegal activities: If someone is using your Wi-Fi network to engage in illegal activities, such as downloading copyrighted material or sharing illegal content, you could be held liable for your actions.
Different software applications to steal your wifi
It is important to remember that stealing someone else’s WiFi password without their permission is a violation of their privacy and can have serious legal consequences.
However, it is worth noting that there are several legitimate software applications that can be used to test the security of your own Wi-Fi network and identify any vulnerabilities that may be exploited by attackers.
These tools are often referred to as WiFi password crackers or security audit tools and are designed to help network administrators and security professionals identify and fix security issues on their own networks.
Examples of legitimate Wi-Fi security audit tools include Aircrack-ng, wifite, Wireshark, and Kali Linux. However, it is important to note that these tools should only be used for legitimate security purposes and not for illegal activities such as hacking into someone else’s Wi-Fi network without their permission.
How to Check If someone stealing your Wi-Fi?
If you suspect that someone may be stealing your Wi-Fi, there are several steps you can take to check and confirm your suspicions:
- Check your router logs: Most Wi-Fi routers keep logs of all the devices that connect to them. Check your router’s log to see if there are any devices connected that you do not recognize.
- Use a network scanner: You can use a network scanner tool to scan your WiFi network and see all the devices that are connected to it. If you notice any unfamiliar devices, it may be a sign that someone is using your network without your permission.
- Monitor your network activity: Use your router’s built-in tools or third-party software to monitor your network activity and see if there is any unusual activity or high data usage that cannot be explained by your own usage patterns.
- Change your WiFi password: If you suspect that someone is stealing your WiFi, one of the easiest ways to stop them is to change your Wi-Fi password. Make sure to choose a strong and complex password that is difficult to guess.
- Enable MAC address filtering: Most WiFi routers allow you to specify which devices are allowed to connect to your network based on their MAC address. You can use this feature to block any unauthorized devices from connecting to your network.
It is important to remember that while it is possible that your neighbors may be stealing your Wi-Fi, there may also be other explanations for slow internet speeds or unusual network activity.
Before accusing your neighbors of stealing your WiFi, make sure to rule out other possible causes and approach the situation with caution and respect.
How to protect your Wi-Fi network from theft?
Fortunately, there are several steps you can take to protect your WiFi network from theft:
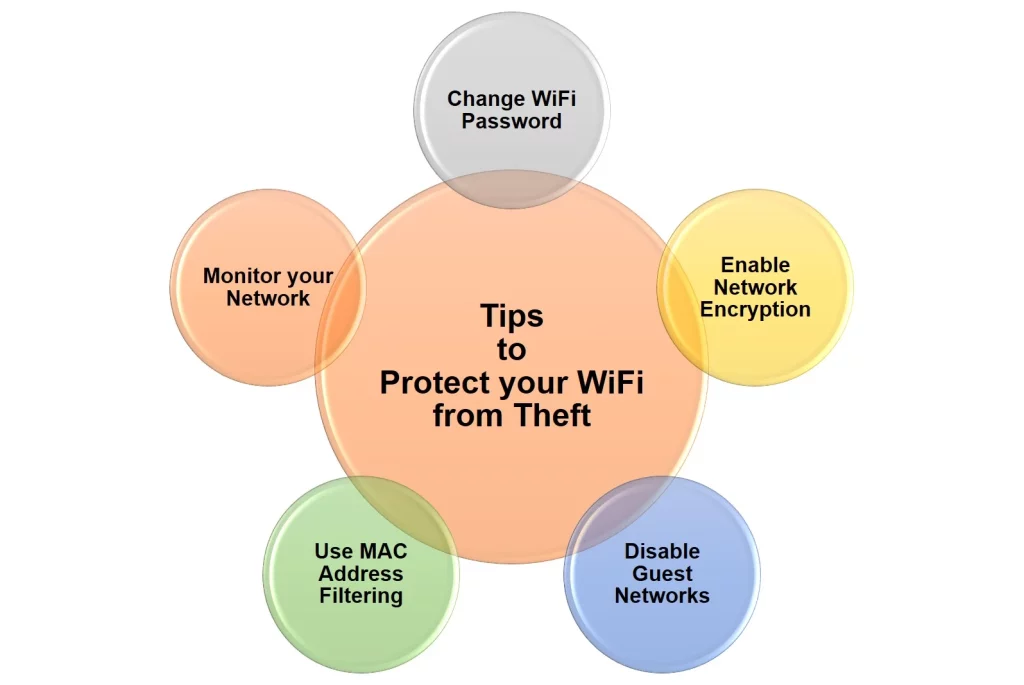
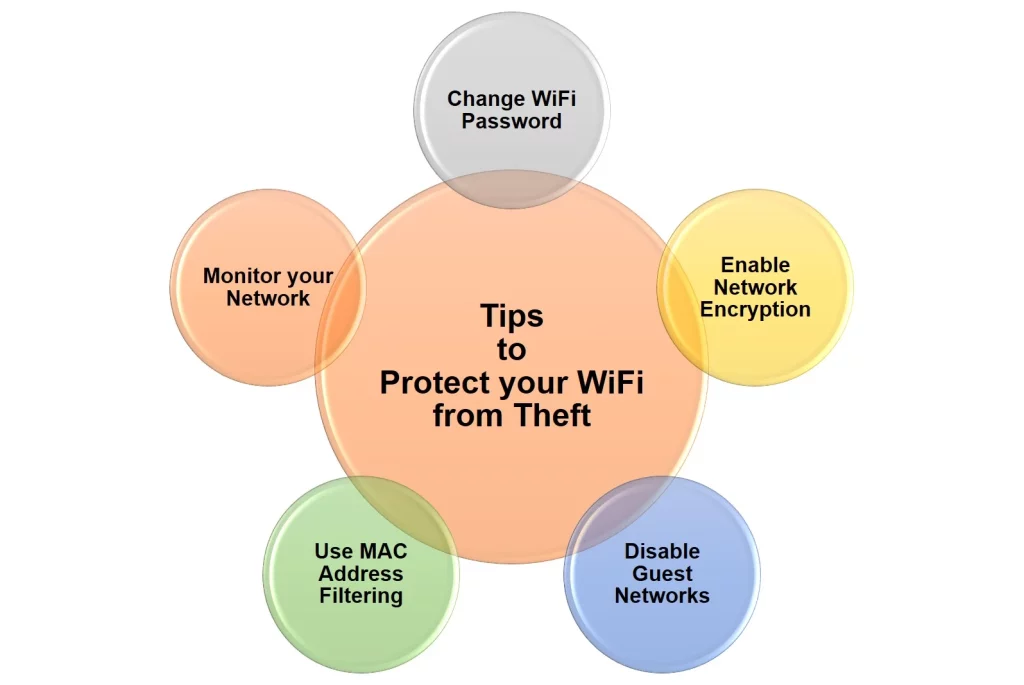
- Change your Wi-Fi password: The first and most important step is to change your Wi-Fi password to something strong and complex. Avoid using common words or phrases, and use a combination of upper and lowercase letters, numbers, and symbols.
- Enable network encryption: Most Wi-Fi routers support encryption, which scrambles the data being transmitted over your network. Make sure to enable this feature and choose the strongest encryption protocol available (such as WPA2).
- Disable guest networks: If your router has a guest network feature, make sure to disable it if you’re not using it. This will prevent unauthorized users from accessing your network.
- Use MAC address filtering: Most Wi-Fi routers allow you to specify which devices are allowed to connect to your network based on their MAC address. This can be an effective way to prevent unauthorized users from connecting to your network.
- Monitor your network: Keep an eye on your network activity to make sure that only authorized devices are connected. Most routers have built-in tools that allow you to monitor your network traffic and view connected devices.
In conclusion, anyone with the right tools and knowledge can steal your WiFi network. However, by following these simple steps, you can significantly reduce the risk of unauthorized access and protect your personal information and network resources.
Remember to always use a strong and complex password, enable encryption, and monitor your network for any suspicious activity.